Microsoft has released security updates (SUs) for vulnerabilities found in:
- Exchange Server 2013
- Exchange Server 2016
- Exchange Server 2019
IMPORTANT: Updates are released in a self-extracting auto-elevating .exe package. Please see this post for more information. Older version of update packages can be downloaded from Microsoft Update Catalog.
These SUs are available for the following specific builds of Exchange Server:
The SUs address vulnerabilities responsibly reported to Microsoft by security partners and found through Microsoft’s internal processes. Although we are not aware of any active exploits in the wild, our recommendation is to immediately install these updates to protect your environment.
These vulnerabilities affect Exchange Server. Exchange Online customers are already protected from the vulnerabilities addressed in these SUs and do not need to take any action other than updating any Exchange servers in their environment.
More details about specific CVEs can be found in the Security Update Guide (filter on Exchange Server under Product Family).
Manual enablement of Windows Extended Protection
Addressing some of CVEs released this month requires admins to enable Windows Extended protection on your Exchange servers. To help you enable this feature, we have developed a script for this process. Please carefully evaluate your environment and review all known issues mentioned in the script documentation before enabling Windows Extended protection on your Exchange servers.
Please note that enabling Extended Protection (EP) is only supported on specific versions of Exchange (please see documentation for full list of prerequisites).
The current version of this script can be found at https://aka.ms/ExchangeEPScript and the documentation is at https://aka.ms/ExchangeEPDoc. For script and documentation changes and suggestions, please engage with us via GitHub to ensure proper issue and change tracking. The script provided to enable Extended Protection will automatically perform an automatic update if the computer on which it is executed has an internet connection (direct or via proxy). However, if you don’t have internet access, make sure to download the latest version of the script as we are continuously improving it.
It is important that you fully understand Windows Extended Protection prerequisites and all known issues before running the script in your environment. Enabling Extended Protection affects communication between your Exchange servers and between clients and servers.
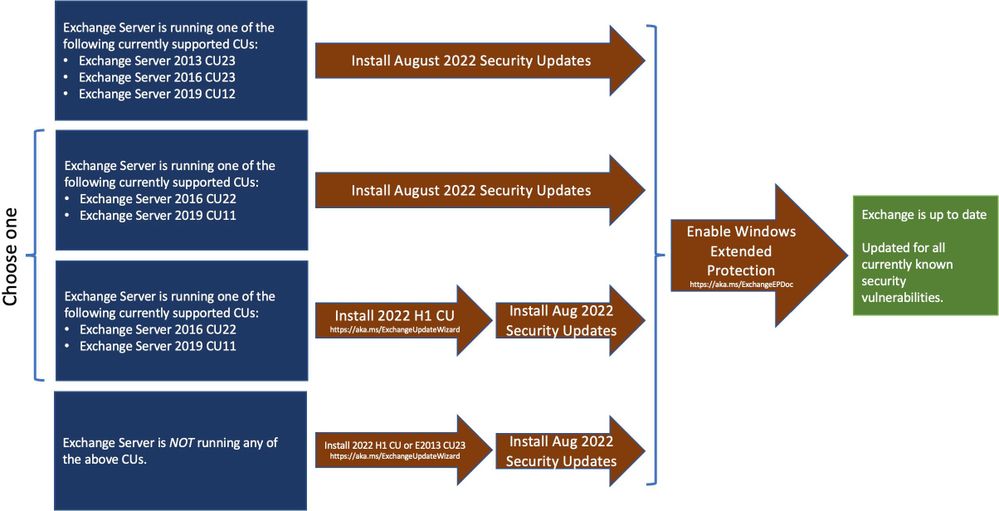
Update installation
Update paths available:
Inventory your Exchange Servers / determine which updates are needed
Use the Exchange Server Health Checker script (use the latest release) to inventory your servers. Running this script will tell you if any of your Exchange Servers are behind on updates (CUs and SUs).
Update to the latest Cumulative Update
Go to https://aka.ms/ExchangeUpdateWizard and choose your currently running CU and your target CU to get directions for your environment.
If you encounter errors during or after installation of Exchange Server updates
If you encounter errors during installation, see the SetupAssist script. If something does not work properly after updates, see Repair failed installations of Exchange Cumulative and Security updates.
Known issues with this release
We are not aware of any known issues with this release.
FAQs
My organization is in Hybrid mode with Exchange Online. Do I need to do anything?
While Exchange Online customers are already protected, the August 2022 SUs do need to be installed on your on-premises Exchange servers, even if they are used only for management purposes. You do not need to re-run the Hybrid Configuration Wizard (HCW) after installing updates.
Do I need to install the updates on ‘Exchange Management Tools only’ workstations?
Servers or workstations running only the Management Tools role (no Exchange services) do not need these updates.
Updates to this post:
- We temporarily removed and now re-added a link to Exchange 2019 CU12 update package because of the issue with original download. The date of publication on the correct package is 8/9/2022.
Read full article (Microsoft Exchange Blog)
All content and images belong to their respected owners, this article is curated for informational purposes only.